January 1, 2024
· 3 min readShhh! It's a Secret: How Keycloak Keeps Your Data Safe
Keycloak is an open-source identity broker: your app delegates login to a central server, gets back tokens, and never has to store passwords itself. This article walks through the login redirect flow, why that pattern is more secure, and where to go next—including Laravel integration.
Have you ever stopped to think about how your favorite websites and apps keep your data safe? It is a fair question, especially when security breaches are routine headline news.
Here is the short version: many products delegate identity to a dedicated server. Keycloak is one of the most widely used open-source options for that job.
That is what this article is about.
TL;DR
- Keycloak is an IAM (identity and access management) server: it handles login, tokens, and policies so your app does not have to be the system of record for passwords.
- The usual flow is redirect → sign-in at Keycloak → token back to the app → access. Your app trusts Keycloak, not a copied password field in its own database.
- Security benefits include strong encryption on the wire, centralized auditing, and consistent rules across many applications.
- If you use Laravel, you can integrate Keycloak via standard OAuth2/OIDC client patterns; there is a walkthrough video below.
What is Keycloak?
Imagine Keycloak as a dedicated gate for identity. It sits between users and your applications: it verifies who someone is and whether they are allowed to do what they are asking to do. Keycloak is open source and speaks standard protocols (OAuth 2.0 and OpenID Connect) that most modern stacks can plug into.
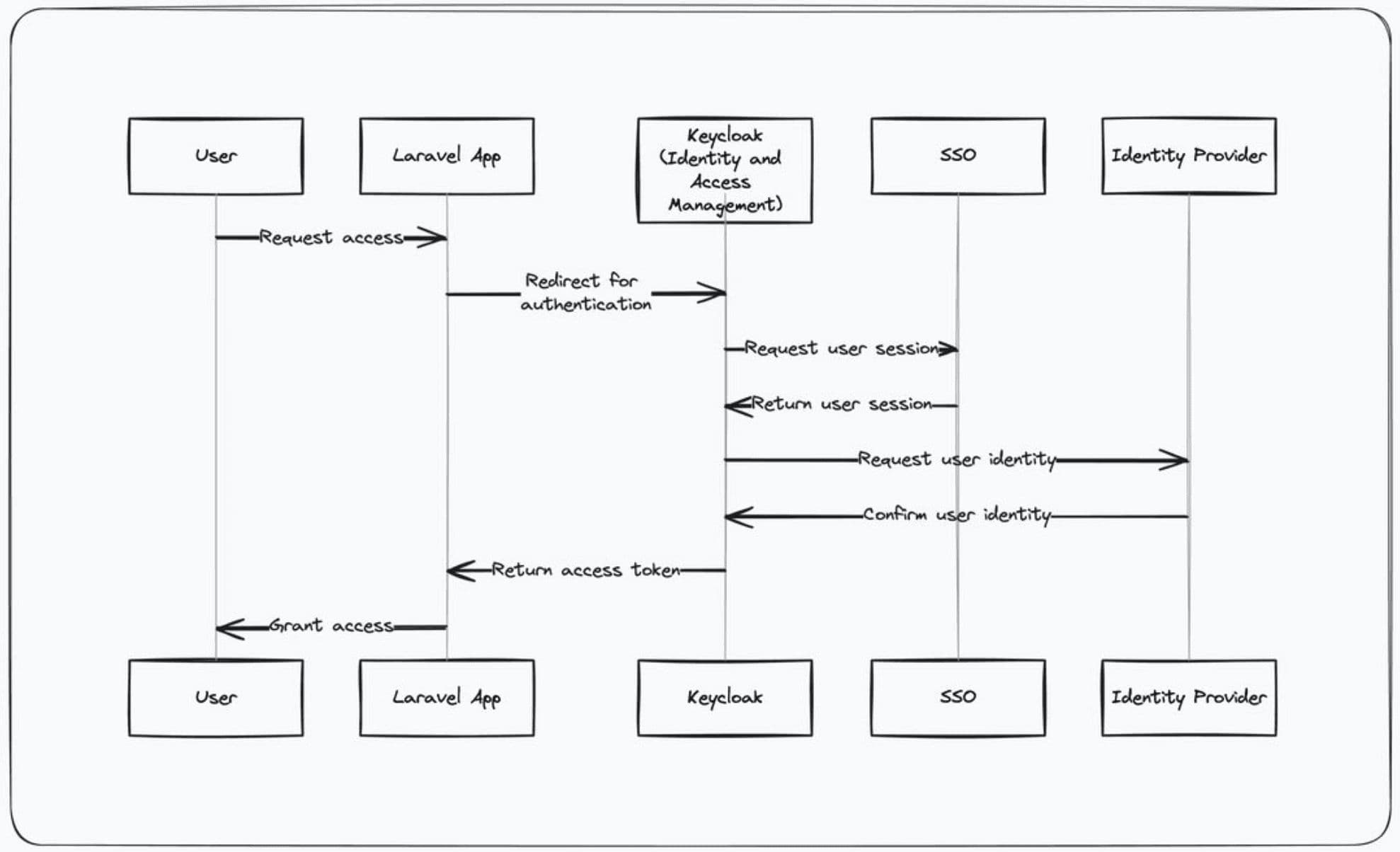
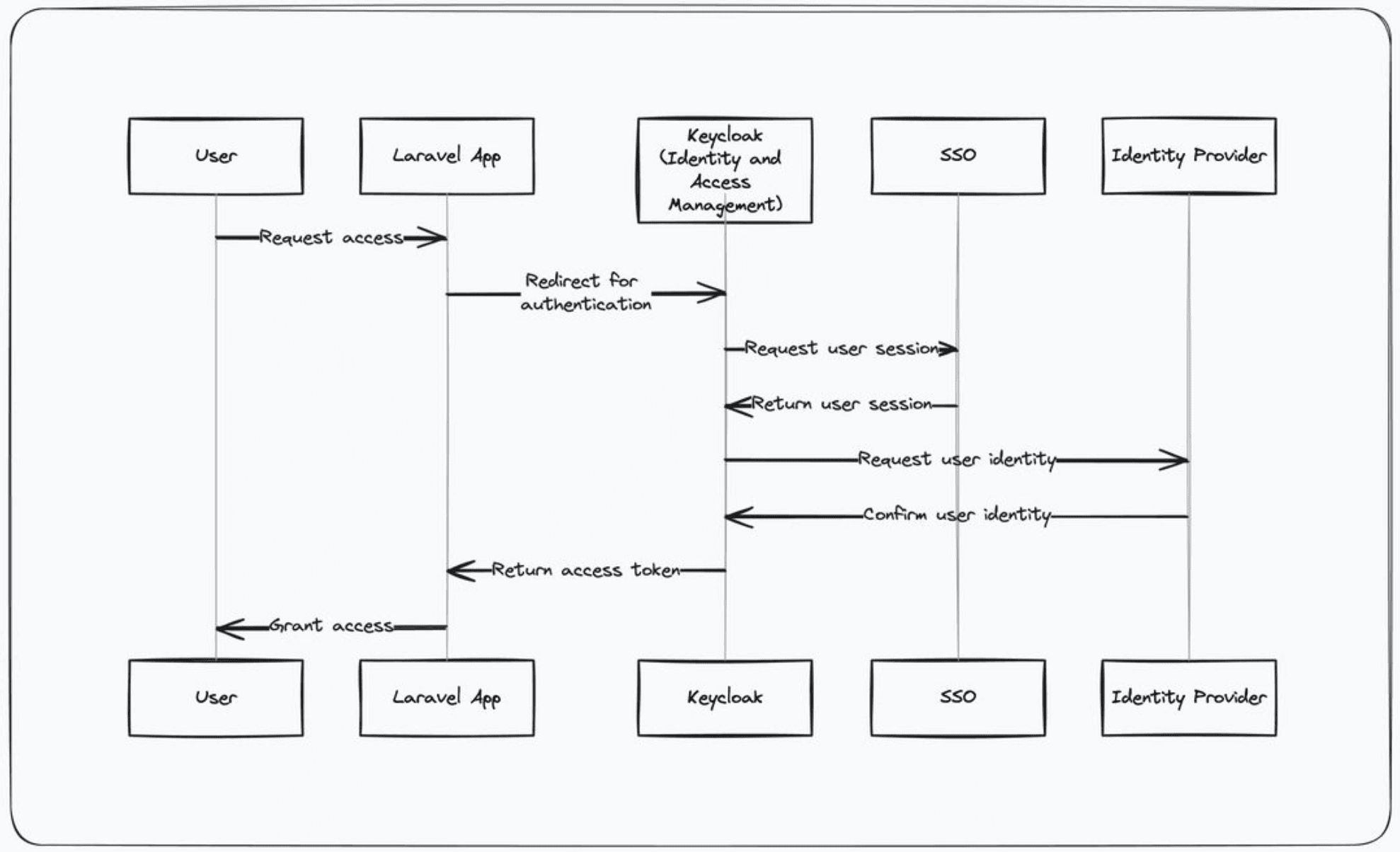
Here is a simplified rundown of how a login works, as illustrated in the diagram below:
- User tries to log in to your app: The application starts an OIDC/OAuth flow and points the browser at Keycloak.
- App redirects to Keycloak: The user enters credentials (and MFA, if configured) on Keycloak’s UI—not on a random form inside your app.
- Keycloak confirms your identity: Keycloak validates the user against its user store or federated identity providers.
- Keycloak gives you a token: Keycloak returns tokens that cryptographically attest identity and entitlements.
- App grants access: Your app validates the token and maps claims to a local session or API authorization.
💡 Tip: If you are explaining this to stakeholders, emphasize one place to harden (Keycloak) instead of N apps each implementing login slightly differently.
Why is Keycloak so secure?
Keycloak can enforce encryption in transit, strong authentication (including MFA), and consistent policy across services. Because credentials are checked at the identity provider, you reduce the chance that a single compromised app leaks the master password database for your product.
It also leaves an audit trail of sign-ins and token issuance, which helps you spot suspicious locations, devices, or brute-force patterns.
How does Keycloak work?
How can I learn more about Keycloak?
If you are a developer who wants to wire Keycloak into a Laravel app, this video walks through a concrete setup:
Conclusion
Central identity is not magic—it is protocols and discipline. Keycloak gives you a maintained, standards-based place to authenticate users and issue tokens; your applications become simpler and safer because they consume those tokens instead of reinventing auth on every new service.
Many products you use every day follow this pattern. Next time you complete a login redirect, you are seeing the same architectural idea in action.
Enjoyed this post? Follow on LinkedIn for more engineering insights.
FAQ
What is Keycloak?
Keycloak is an open-source identity and access management (IAM) server. Applications send users to Keycloak for login; Keycloak verifies credentials and issues tokens so apps can trust who the user is without holding the password themselves.
Why does the app redirect you to Keycloak to log in?
The redirect keeps credential entry on a dedicated, hardened host. Your application never sees the raw password at login time, which reduces leak surface and lets you enforce MFA, policies, and auditing in one place.
What are tokens used for after login?
After Keycloak confirms identity, it issues tokens (often JWT-style) that act like proof of session. The app validates those tokens with Keycloak or using its public keys, then grants access based on roles and scopes encoded in the token.
How is Keycloak different from building auth inside my app?
Centralizing auth means one system for users, sessions, password resets, and compliance across many services. Each app becomes an OAuth/OIDC client instead of reimplementing login, password hashing, and session stores.
Can I use Keycloak with Laravel?
Yes. Laravel apps typically use an OAuth2/OIDC client package or socialite-style flow to send users to Keycloak and consume tokens on callback. The video linked at the end of this post demonstrates a practical Laravel-oriented setup.