Loading…
Tag
#Security
6 posts

June 8, 2026
The Ticking Clock: Why Short-Lived JWTs Are Your Best Defense
Stateless JWTs can't be revoked on demand — once issued, they live until they expire. This deep dive covers why short lifetimes (5–15 min) are the strongest control you have, how the access/refresh token split actually works, refresh token rotation with reuse detection, and the sender-constrained token guidance from RFC 9700 (Jan 2025).
JWTAuthenticationSecurity

June 3, 2026
Backend-for-Frontend (BFF): The Missing Piece in Your Fullstack App
Your frontend is doing too much — orchestrating microservices, parsing messy payloads, and worst of all, holding auth tokens the browser can't keep safe. The Backend-for-Frontend pattern moves all of that to a server layer you control. Here's why it matters (especially after the September 2025 npm attack that hit packages with 2.6B weekly downloads) and how Next.js gives you one for free.
Next.jsArchitectureSecurity
May 22, 2026
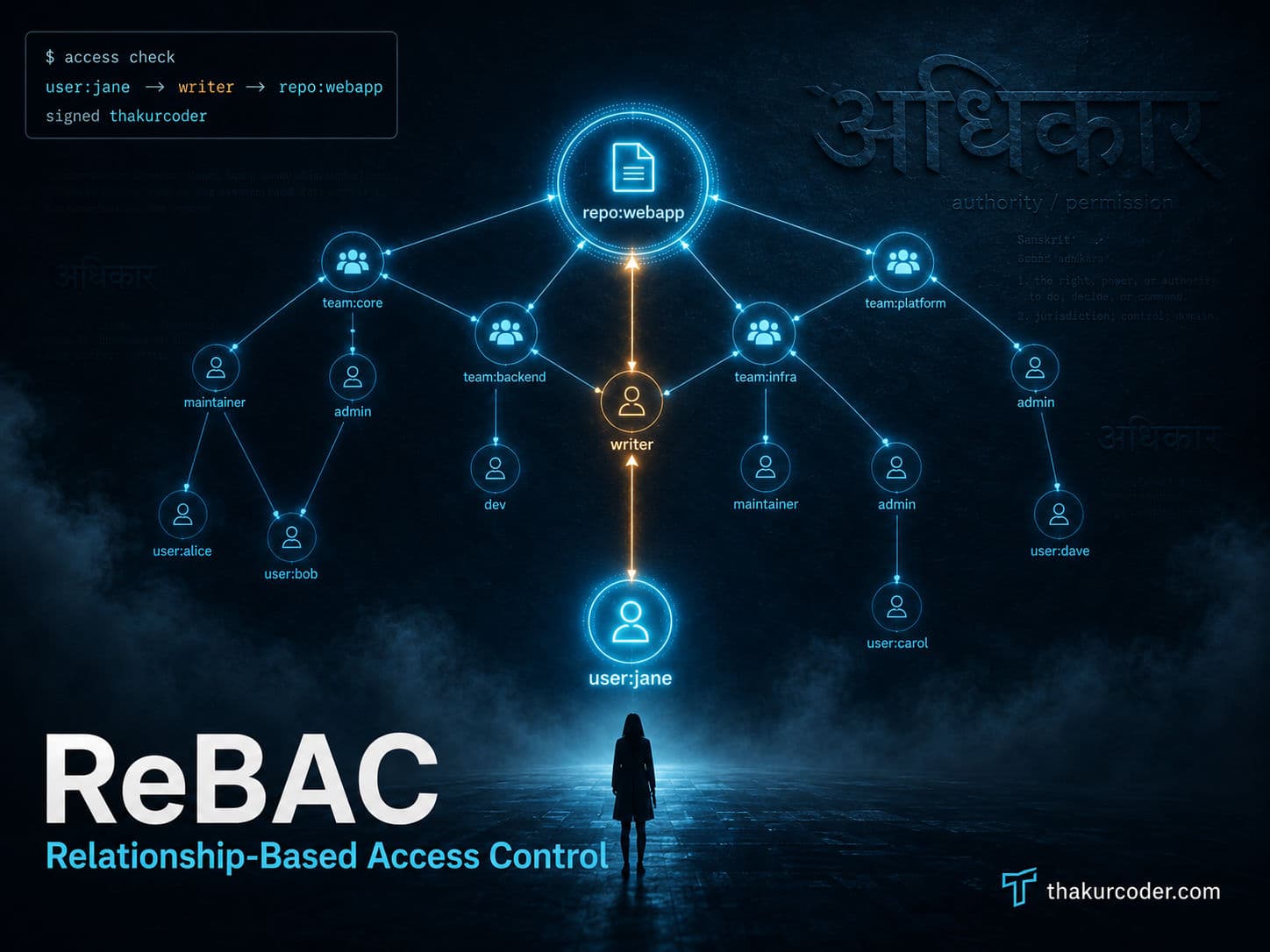
ReBAC Explained: How GitHub Decides Who Can Touch Your Repo
Roles work until your app grows hierarchies, then you drown in role explosion and token bloat. Relationship-Based Access Control (ReBAC) answers 'can this user do this?' by walking a graph of relationships instead. This post explains ReBAC using GitHub's permission model as the main example, then covers Google Zanzibar — which manages over 2 trillion relationship tuples at 10 million queries per second.
AuthorizationReBACSystem Design

April 17, 2026
31 WordPress Plugins, One Flippa Sale, and an 8-Month Time Bomb
In April 2026, WordPress.org closed 31 plugins after an attacker bought a trusted plugin portfolio on Flippa, shipped a dormant PHP deserialization backdoor, and activated it eight months later — with command-and-control resolved through an Ethereum smart contract. This post breaks down how the attack actually worked, why 96% of WordPress vulnerabilities live in plugins, and how Cloudflare's new EmDash CMS attempts to fix the architecture with capability-scoped sandboxes.
WordPressSupply Chain AttackSecurity

April 1, 2026
100 Million Downloads. One Compromised Account. Your Machine Is Now a Botnet.
On March 31, 2026, two malicious versions of Axios — axios@1.14.1 and axios@0.30.4 — were discovered containing a precision-engineered, self-erasing supply chain attack. The RAT it dropped could silently steal your AWS credentials, API keys, and more — and npm audit reported a clean bill of health the entire time. Here's exactly how it worked.
SecuritynpmJavaScript
January 1, 2024
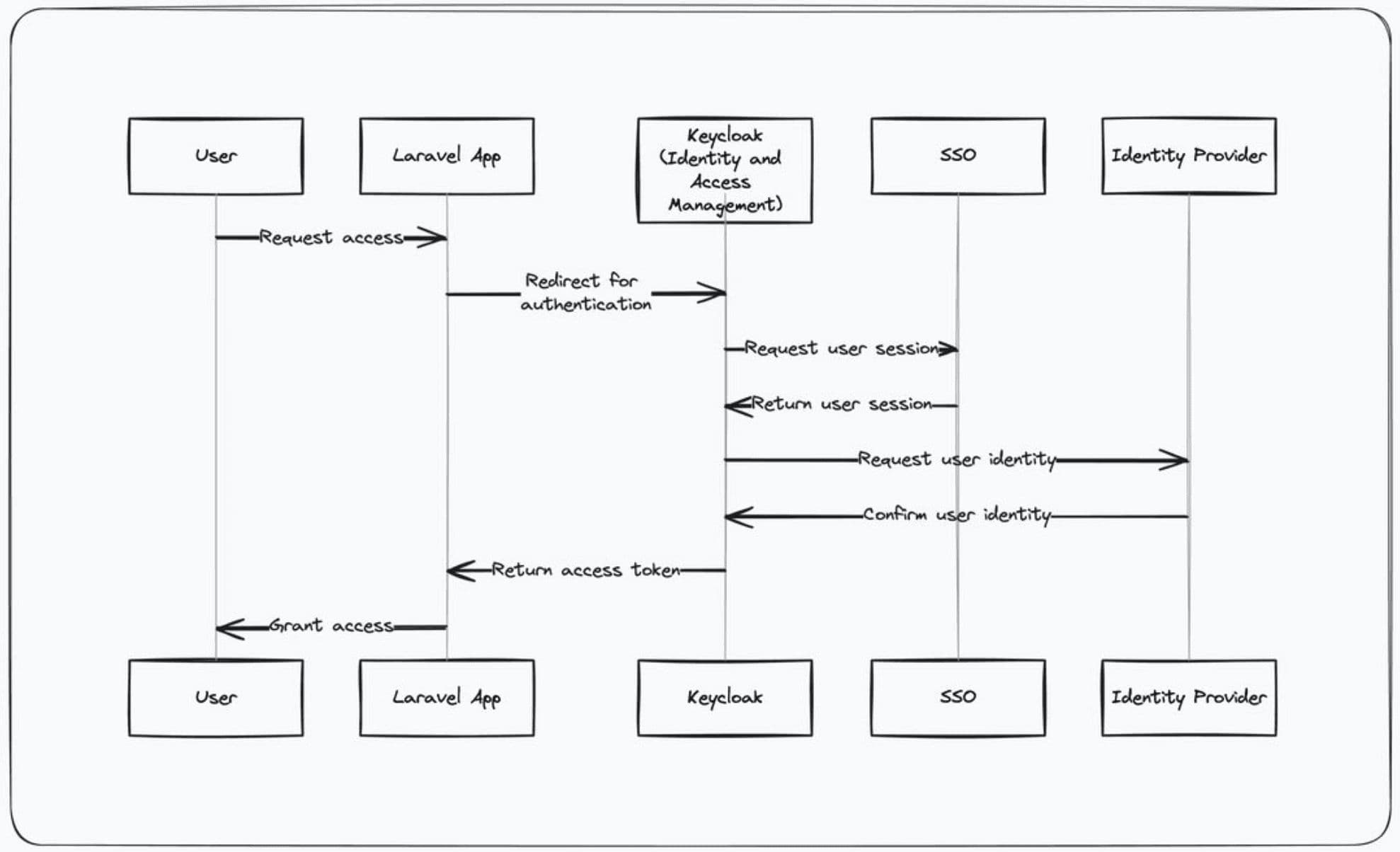
Shhh! It's a Secret: How Keycloak Keeps Your Data Safe
Keycloak is an open-source identity broker: your app delegates login to a central server, gets back tokens, and never has to store passwords itself. This article walks through the login redirect flow, why that pattern is more secure, and where to go next—including Laravel integration.
KeycloakIAMOAuth